Introduction to 127.0.0.1:62893
In networking, certain terminology and addresses remain vital and shape the way computers communicate within a community. One such agreement is 127.0.0.1:62893, which is a mixture of the local host IP address and the selected port number. This newsletter dives into the importance of this agreement, its position in networks, and how it helps various applications and services.
What is 127.0.0.1?
The address is 127.0.0.1, usually called localhost and is the community loopback interface on the computer. Far is used to establish an IP connection to the same system or computer used by a stop-user. Essentially, it allows the device to talk to itself, which is beneficial for checking and improving features.
While the laptop points to 127.0.0.1, it is now not subject to the outside community. Rather, it stays on the machine, allowing developers and network administrators to check their programs locally before deploying them to servers. This technique is efficient, and secure, and allows comprehensive tuning without the risks associated with operating outside the community.
Port number function
Port numbers are essential for community communication and serve as endpoints for various offers and packages. Even though it is married to IP, the number of ports allows you to direct visitors to the ideal tool on the server. In the context of 127.0.0.1:62893, 62893 is a port variant that indicates the selected service or software is traversing a local host.
Port numbers range from 0 to 65535, with positive degrees reserved for exact protocols and menus. The 62893 variety falls into a class of dynamic or non-public ports that are generally used by programs for their own or temporary purposes. These ports are not assigned to any specific service, allowing developers to use them for various testing options.
Meaning 127.0.0.1:62893 for improvement
For software developers and community engineers, 127.0.0.1:62893 offers a sandbox environment where they can run and review programs without affecting resident systems. This environmental control is crucial for several reasons:
- Isolation: the walking programs at 127.0.0.1:62893 guarantee that any problems or errors will now not manifest outside of customers or systems. This isolation is essential for debugging and improving software before it goes into production.
- Overall Performance Testing: By using 127.0.0.1:62893 developers can measure the overall performance of their applications under many conditions. This close setup allows them to tune configurations and optimize overall performance without the noise of network latency or outside visitors.
- Protection: logging out on a local host minimizes security risks. Because the verbal exchange remains inside the nearby gadget, there is no exposure to external threats, making it a convenient environment for testing sensitive programs.
- Configuration: Creators can configure their packages to pay attention to 127. Zero.0.1:62893 and make sure they are best at hand from a local gadget. This setting is useful for developing offers that may be private or limited to unique customers.
Realistic Applications 127.0.0.1:62893
- Internet Improvement: In Internet improvement, using 127.0.0.1:62893 allows developers to run a nearby server to test websites and Internet packages. Appliances like Apache, Nginx, or custom network servers can be configured to listen to this agreement and port, providing a secure environment to build and test before it goes live.
- Database Management: Databases along with MySQL, PostgreSQL, or MongoDB can be sure that 127.0.0.1:62893 for the neighborhood will get access. This setting is particularly beneficial during the development and testing phases, as it ensures that database queries and operations do not affect residency data.
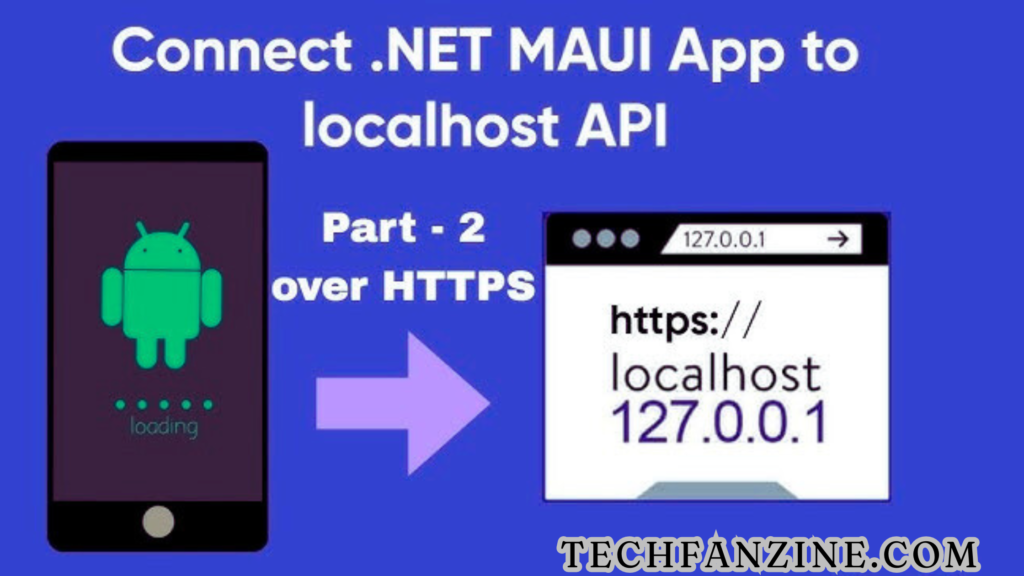
- APIs and microservices: With the growing trend of microservices architecture, developers often run more than one offering on different local host ports. Binding the API service to 127.0.0.1:62893 allows seamless integration and testing of conversations between services without external dependencies.
- Application Debugging: Debug devices and environments can be configured to use 127.0.0.1:62893, allowing developers to walk through code, inspect variables, and examine software behavior in a controlled environment.
Configuring packages to use 127.0.0.1:62893
Embedding the software for 127.0.0.1:62893 requires several configuration steps, usually specific to the tool settings or configuration documents. Here is the fashionable method:
- Regulate configuration documents: programs regularly have configuration documents in which the IP copy and port number are specified. By setting the IP to 127.0.0.1 and the port to 62893, the software will focus on the desired nearby connection and port.
- Command line parameters: several programs allow you to specify the IP and port using command line arguments. For example, a walk through an internet server might look like this:
Replica code
Python -m http. Server –bind127.0.0.1:62893
- Environment variables: Another approach is to use environmental variables to set the IP and port. This approach is common in containerized environments such as Docker, where configuration is often managed through environment variables.7
Troubleshooting 127.0.0.1:62893
Despite its simplicity, problems can arise when working with 127.0.0.1:62893. Here are the common problems and their answers:
- Port conflicts: If port 62893 is already in use by another tool, the brand-new software may not be able to bind to it. To fix this problem, discover the conflicting software and prevent it, or choose a one-of-a-kind port.
- Firewall settings: Neighborhood firewall settings can block website visitors on positive ports. Make sure your firewall allows port 62893 for local hosts’ visitors.
- Application errors: Misconfiguration or errors inside the software can prevent binding to 127.0.0.1:62893. Look at the tool’s error logs to make sure the IP and port are specified correctly.
- Regulations for operating equipment: several operating systems have regulations or dedicated ports. Confirm that 62893 is not always reserved and is available for use in your operating system.

Conservation concerns
While 127.0.0.1:62893 is inherently relaxed due to its neighborly nature, there are still some safeguards to keep in mind:
- Access management: make sure sensitive packages are well secured even on the local host. Use authentication and authorization mechanisms to protect yourself from unauthorized access.
- Daily Updates: keep your upgrade and gear environment up-to-date with current security patches and updates.
- Network Isolation: In a shared enhancement environment, ensure that 127. Zero. Zero.1:62893 programs are not on hand with the help of different customers, unless they are supposed to be.
- Data encryption: For packages handling sensitive facts, remember to encrypt the conversation even on the local host to avoid accidental fact leaks.
Fate of Localhost usage and ports
The use of local hosts and specific ports such as 127.0.0.1:62893 will continue to be the basis of the development and testing environment. With increasing application complexity and the rise of containerization and microservices, a reliable and isolated on-premises environment is more important than ever.
Additionally, advances in virtualization and field technologies will beautify the way builders use local hosts. Gear like Docker and Kubernetes already make noticeable use of local hosts for local tweaking and testing. As these technologies evolve, the potential to seamlessly switch between near and distant environments will improve, making the development process greener and more convenient.
Conclusion
Cope with127.0.0.1:62893 represents more than just an IP and port combination; it symbolizes the core of nearby development and sign-off. Its function in offering a cozy, remote, and efficient environment is essential for developers and network engineers. Information about their importance and their effective use could greatly enhance the life cycle of improvement, from preliminary testing to final deployment.
Whether you are an experienced developer or just starting, learning with 127.0.0.1:62893 is sure to help you create robust, convenient, and environmentally friendly programs. As technology advances, this basic idea will remain the cornerstone of powerful software development practices.
(FAQs)
1. What is 127.0? Zero.1?
Answer: 127. Zero.0.1 is the loopback address, usually referred to as localhost. It is used by a computer to talk to itself and provides a way to check and extend packages locally without using an external network.
2. What is the wide range of 62893 ports?
Solution: Port number 62893 is a dynamic or non-public port used by packages to establish channels for verbal exchange. It is not reserved for any unique service, allowing builders to use it for their own or temporary purposes.
3. Why would a developer use 127.0.0.1:62893?
Answer: Developers use 127.0.0.1:62893 to create a secure remote environment for testing and debugging applications. This setup ensures that no issues or bugs affect live builds and allows for performance optimization without outside community intervention.
4. How do I configure my tool to use 127.0.0.1:62893?
Solution: Configuring an application to use 127.0.0.1:62893 usually involves editing configuration files, using command line parameters, or setting environmental variables. For instance, you can specify the IP and port agreement in the application configuration assembly, or bypass them as arguments when starting the software.
5. What are the unusual problems with using 127.0.0.1:62893?
A: Common problems include port conflicts (when every other software uses the identical port), firewall settings blocking the port, software bugs or misconfigurations, and port usage restrictions on production machines.
6. How can I check if port 62893 is in use?
Answer: you can test if port 62893 is in use by running the commands together with netstat or lsof on Unix-based builds or netstat -and on Windows. These instructions list the power connections and ports that applications use.